Substitution cipher: Difference between revisions
en>ClueBot NG m Reverting possible vandalism by 117.207.220.153 to version by CountingPine. False positive? Report it. Thanks, ClueBot NG. (1192322) (Bot) |
en>TedColes m Undid revision 590935193 by 118.102.164.202 (talk) |
||
| Line 1: | Line 1: | ||
{{Featured article}} | |||
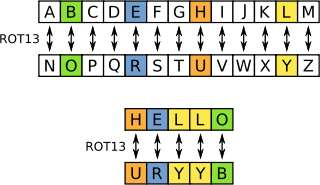
[[Image:ROT13 table with example.svg|right|thumbnail|320px|ROT13 replaces each letter by its partner 13 characters further along the alphabet. For example, <tt>HELLO</tt> becomes <tt>URYYB</tt> (or, reversing, <tt>URYYB</tt> becomes <tt>HELLO</tt> again).]] | |||
'''ROT13''' ("'''rotate by 13 places'''", sometimes hyphenated '''ROT-13''') is a simple letter [[substitution cipher]] that replaces a letter with the letter 13 letters after it in the alphabet. ROT13 is an example of the [[Caesar cipher]], developed in ancient Rome. | |||
In the [[ISO basic Latin alphabet|basic Latin alphabet]], ROT13 is its own [[inverse function|inverse]]; that is, to undo ROT13, the same algorithm is applied, so the same action can be used for encoding and decoding. The algorithm provides virtually no [[cryptography|cryptographic]] security, and is often cited as a canonical example of weak encryption. | |||
ROT13 is used in [[online forum]]s as a means of hiding [[spoiler (media)|spoiler]]s, [[punch line|punchlines]], puzzle solutions, and [[profanity|offensive material]]s from the casual glance. ROT13 has been described as the "[[Usenet]] equivalent of a magazine [[Transformation of text|printing the answer to a quiz upside down]]".<ref>{{Cite web|first=Bruce|last=Horrocks|url=http://groups.google.com/groups?selm=UZ36hgCSoh%24%2BEwqG%40nodomain.nodomain.us |title=UCSM Cabal Circular #207-a |accessdate=2007-09-17 |date=28 June 2003 |work=[[Usenet]] group uk.comp.sys.mac (Message ID UZ36hgCSoh$+EwqG@nodomain.nodomain.us) }}</ref> ROT13 has inspired a variety of letter and word games on-line, and is frequently mentioned in [[newsgroup]] conversations. | |||
==Description== | |||
Applying ROT13 to a piece of text merely requires examining its alphabetic characters and replacing each one by the letter 13 places further along in the [[alphabet]], wrapping back to the beginning if necessary.<ref name="schneier">{{Cite book|last=Schneier |first=Bruce |authorlink= Bruce Schneier |editor= |others= |title=Applied Cryptography |edition=Second|year=1996|publisher=John Wiley & Sons |isbn= 0-471-11709-9|pages=11 }}</ref> | |||
<tt>A</tt> becomes <tt>N</tt>, <tt>B</tt> becomes <tt>O</tt>, and so on up to <tt>M</tt>, which becomes <tt>Z</tt>, then the sequence continues at the beginning of the alphabet: <tt>N</tt> becomes <tt>A</tt>, <tt>O</tt> becomes <tt>B</tt>, and so on to <tt>Z</tt>, which becomes <tt>M</tt>. Only those letters which occur in the [[English alphabet]] are affected; numbers, symbols, whitespace, and all other characters are left unchanged. Because there are 26 letters in the English alphabet and 26 = 2 × 13, the ROT13 function is its own [[inverse function|inverse]]:<ref name="schneier"/> | |||
:<math>\mbox{ROT}_{13}(\mbox{ROT}_{13}(x))=x</math> for any basic Latin-alphabet text ''x''. | |||
In other words, two successive applications of ROT13 restore the original text (in [[mathematics]], this is sometimes called an ''[[involution (mathematics)|involution]]''; in cryptography, a ''[[reciprocal cipher]]''). | |||
The transformation can be done using a [[lookup table]], such as the following: | |||
{| style="margin-left:auto; margin-right:auto" class="wikitable" | |||
| <tt>ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz</tt> | |||
|- | |||
| <tt>NOPQRSTUVWXYZABCDEFGHIJKLMnopqrstuvwxyzabcdefghijklm</tt> | |||
|} | |||
For example, in the following joke, the punchline has been obscured by ROT13: | |||
How can you tell an extrovert from an | |||
introvert at [[National Security Agency|NSA]]? Va gur ryringbef, | |||
gur rkgebireg ybbxf ng gur BGURE thl'f fubrf. | |||
Transforming the entire text via ROT13 form, the answer to the joke is revealed: | |||
Ubj pna lbh gryy na rkgebireg sebz na | |||
vagebireg ng AFN? In the elevators, | |||
the extrovert looks at the OTHER guy's shoes. | |||
A second application of ROT13 would restore the original. | |||
==Usage== | |||
ROT13 was in use in the net.jokes [[newsgroup]] by the early 1980s.<ref>Early uses of ROT13 found in the Google USENET archive date back to 8 October 1982, posted to the <tt>net.jokes</tt> newsgroup [http://groups.google.com/groups?selm=bnews.desoto.299][http://groups.google.com/groups?selm=bnews.utcsrgv.596].</ref> It is used to hide potentially offensive jokes, or to obscure an answer to a puzzle or other [[spoiler (media)|spoiler]].<ref name="schneier"/><ref name="jargon">{{Cite web|date= 2003-12-29|first=Eric S. (ed.)|last=Raymond|authorlink=Eric S. Raymond|url=http://www.catb.org/~esr/jargon/html/R/rot13.html |title=ROT13 |accessdate=2007-09-19 |work=The Jargon File, 4.4.7 }}</ref> A shift of thirteen was chosen over other values, such as three as in the original [[Caesar cipher]], because thirteen is the value for which encoding and decoding are equivalent, thereby allowing the convenience of a single command for both.<ref name="jargon"/> ROT13 is typically supported as a built-in feature to newsreading software.<ref name="jargon"/> Email addresses are also sometimes encoded with ROT13 to hide them from less sophisticated [[spam bots]]. | |||
ROT13 is an example of the [[encryption algorithm]] known as a [[Caesar cipher]], attributed to [[Julius Caesar]] in the 1st century BC.<ref>{{Cite book|last=Kahn |first=David |authorlink=David Kahn (writer) |coauthors= |title=The Codebreakers: The Story of Secret Writing |year= |publisher=Macmillan |location=New York |isbn=0-684-83130-9 }}</ref> | |||
ROT13 is not intended to be used where [[confidentiality|secrecy]] is of any concern—the use of a constant shift means that the encryption effectively has no [[key (cryptography)|key]], and decryption requires no more knowledge than the fact that ROT13 is in use. Even without this knowledge, the algorithm is easily broken through [[Frequency analysis (cryptanalysis)|frequency analysis]].<ref name="schneier"/> Because of its utter unsuitability for real secrecy, ROT13 has become a catchphrase to refer to any conspicuously weak [[encryption]] scheme; a critic might claim that "56-bit [[Data Encryption Standard|DES]] is little better than ROT13 these days". Also, in a play on real terms like "double DES", the terms "double ROT13", "ROT26", or "2ROT13" crop up with humorous intent, including a spoof academic paper "On the 2ROT13 Encryption Algorithm".<ref>{{Cite web|title=On the 2ROT13 Encryption Algorithm|format=PDF|date=2004-09-25 |url=http://www.pruefziffernberechnung.de/Originaldokumente/2rot13.pdf|publisher=Prüfziffernberechnung in der Praxis|accessdate=2007-09-20}}</ref> As applying ROT13 to an already ROT13-encrypted text restores the original [[plaintext]], ROT26 is equivalent to no encryption at all. By extension, triple-ROT13 (used in joking analogy with 3DES) is equivalent to regular ROT13. | |||
In December 1999, it was found that [[Netscape Communicator]] used ROT-13 as part of an insecure scheme to store email passwords.<ref>{{Cite web|author=Hollebeek, Tim|coauthors=[[John Viega|Viega, John]]|url=http://citeseer.ist.psu.edu/500396.html |publisher=Reliable Software Technologies|title=Bad Cryptography in the Netscape Browser: A Case Study|accessdate=2007-09-20}}</ref> In 2001, Russian programmer [[Dimitry Sklyarov]] demonstrated that an eBook vendor, New Paradigm Research Group (NPRG), used ROT13 to encrypt their documents; it has been speculated that NPRG may have mistaken the ROT13 toy example—provided with the [[Adobe Systems|Adobe]] eBook [[software development kit]]—for a serious encryption scheme.<ref>{{Cite web|first=Bruce|last=Perens|authorlink=Bruce Perens|url=http://www.zdnet.com/news/dimitry-sklyarov-enemy-or-friend/116424 |title=Dimitry Sklyarov: Enemy or friend?|date=2001-09-01|accessdate=2011-02-03|publisher=[[ZDNet News]]}}</ref> Windows XP uses ROT13 on some of its registry keys.<ref>{{Cite web|first=Vic|last=Ferri |title=The Count Keys in the Windows Registry|url=http://www.personal-computer-tutor.com/abc3/v29/vic29.htm|publisher=ABC: All 'Bout Computers|date=2007-01-04|accessdate=2007-09-20}}</ref> | |||
The ROT13 encryption is used to cipher cache hints on [[Geocaching]].com. | |||
==Letter games and net culture== | |||
{| class="wikitable" align="right" style="margin: 0 0 1em 1em; text-align: center" | |||
|- | |||
| colspan="2" | <tt>abcdefghijklmnopqrstuvwxyz</tt><br /><tt>NOPQRSTUVWXYZABCDEFGHIJKLM</tt> | |||
|- | |||
| <tt>aha</tt> ↔ <tt>nun</tt> || <tt>ant</tt> ↔ <tt>nag</tt> | |||
|- | |||
| <tt>balk</tt> ↔ <tt>onyx</tt> || <tt>bar</tt> ↔ <tt>one</tt> | |||
|- | |||
| <tt>barf</tt> ↔ <tt>ones</tt> || <tt>be</tt> ↔ <tt>or</tt> | |||
|- | |||
| <tt>bin</tt> ↔ <tt>ova</tt> || <tt>ebbs</tt> ↔ <tt>roof</tt> | |||
|- | |||
| <tt>envy</tt> ↔ <tt>rail</tt> || <tt>er</tt> ↔ <tt>re</tt> | |||
|- | |||
| <tt>errs</tt> ↔ <tt>reef</tt> || <tt>flap</tt> ↔ <tt>sync</tt> | |||
|- | |||
| <tt>fur</tt> ↔ <tt>she</tt> || <tt>gel</tt> ↔ <tt>try</tt> | |||
|- | |||
| <tt>gnat</tt> ↔ <tt>tang</tt> || <tt>irk</tt> ↔ <tt>vex</tt> | |||
<!-- Nice ones: --> | |||
|- | |||
| <tt>clerk</tt> ↔ <tt>pyrex</tt> || <tt>purely</tt> ↔ <tt>cheryl</tt> | |||
|- | |||
| <tt>PNG</tt> ↔ <tt>cat</tt> || <tt>SHA</tt> ↔ <tt>fun</tt> | |||
|- | |||
| <tt>furby</tt> ↔ <tt>sheol</tt> || <tt>terra</tt> ↔ <tt>green</tt> | |||
|- | |||
| <tt>what</tt> ↔ <tt>Jung</tt> || <tt>URL</tt> ↔ <tt>hey</tt> | |||
|- | |||
| <tt>purpura</tt> ↔ <tt>Chechen</tt> || <tt>shone</tt> ↔ <tt>FUBAR</tt> | |||
|- | |||
| <tt>Ares</tt> ↔ <tt>Nerf</tt> || <tt> abjurer</tt> ↔ <tt>nowhere</tt> | |||
|} | |||
ROT13 provides an opportunity for [[letter games]]. Some words will, when transformed with ROT13, produce another word. The longest{{fact|date=September 2013}} example in the [[English language]] is the pair of 7-letter words ''[[wiktionary:abjurer|abjurer]]'' and ''nowhere''; there is also the 7-letter pair ''[[Chechen people|Chechen]]'' and ''[[wiktionary:purpura|purpura]]''. Other examples of words like these are shown in the table.<ref>{{Cite web|url= http://www.furrfu.org/rot13words.html |last=De Mulder|first=Tom|title= ROT13 Words|accessdate=2007-09-19 |work=Furrfu!}}</ref> The pair ''[[gnat]]'' and ''tang'' are an interesting example which are both ROT13 reciprocals and (taken together) a [[palindrome]]. | |||
The 1989 [[International Obfuscated C Code Contest]] (IOCCC) included an entry by Brian Westley. Westley's [[computer program]] can be encoded in ROT13 or reversed and still [[compiler|compiles]] correctly. Its operation, when executed, is either to perform ROT13 encoding on, or to reverse its input.<ref>{{Cite web| url = http://www.ioccc.org/1989/westley.c | title = westley.c | work = [[IOCCC]] | year = 1989 | first = Brian | last = Westley |accessdate=2007-08-13}}</ref> | |||
The newsgroup alt.folklore.urban coined a word—''furrfu''—that was the ROT13 encoding of the frequently encoded utterance "[[:wikt:sheesh|sheesh]]". "<tt>Furrfu</tt>" evolved in mid-1992 as a response to postings repeating [[urban myth]]s on alt.folklore.urban, after some posters complained that "Sheesh!" as a response to [[newbie|newcomer]]s was being overused.<ref>{{Cite web|url=http://foldoc.doc.ic.ac.uk/foldoc/foldoc.cgi?furrfu |title=Furrfu |publisher=[[Foldoc]] |date=1995-10-25 |accessdate=2007-08-13}}</ref> | |||
==Variants== | |||
ROT5 is a practice similar to ROT13 that applies to numeric digits (0 to 9). ROT13 and ROT5 can be used together in the same message. | |||
ROT47 is a derivative of ROT13 which, in addition to scrambling the basic letters, also treats numbers and common symbols. Instead of using the sequence <tt>A–Z</tt> as the alphabet, ROT47 uses a larger set of characters from the common [[character encoding]] known as [[ASCII]]. Specifically, the 7-bit printable characters, excluding space, from decimal 33 '<tt>!</tt>' through 126 '<tt>~</tt>', 94 in total, taken in the order of the numerical values of their ASCII codes, are rotated by 47 positions, without special consideration of case. For example, the character <tt>A</tt> is mapped to <tt>p</tt>, while <tt>a</tt> is mapped to <tt>2</tt>. The use of a larger alphabet produces a more thorough obfuscation than that of ROT13; for example, a telephone number such as <tt>+1-415-839-6885</tt> is not obvious at first sight from the scrambled result <tt>Z`\c`d\gbh\eggd</tt>. On the other hand, because ROT47 introduces numbers and symbols into the mix without discrimination, it is more immediately obvious that the text has been enciphered. | |||
Example: | |||
:<tt>The Quick Brown Fox Jumps Over The Lazy Dog.</tt> | |||
enciphers to | |||
:<tt>%96 "F:4< qC@H? u@I yF>AD ~G6C %96 {2KJ s@8]</tt> | |||
The [[GNU C library]], a set of standard routines available for use in [[computer programming]], contains a [[function (programming)|function]]—'''<tt>memfrob()</tt>'''<ref>{{Cite web|url=http://www.gnu.org/software/libc/manual/html_node/Trivial-Encryption.html|date=2006-12-03|title=5.10 Trivial Encryption|work=The GNU C Library Reference Manual |publisher=[[Free Software Foundation]]|accessdate=2007-09-20}}</ref>—which has a similar purpose to ROT13, although it is intended for use with arbitrary binary data. The function operates by combining each [[byte]] with the [[Binary number|binary]] pattern 00101010 ([[42 (number)|42]]) using the [[exclusive or]] (XOR) operation. This effects a [[simple XOR cipher]]. Like ROT13, <tt>memfrob()</tt> is self-reciprocal, and provides a similar, virtually absent, level of security. | |||
==Implementation== | |||
The ROT13 and ROT47 are fairly easy to implement using the Unix terminal application <tt>[[Tr (Unix)|tr]]</tt>; to encrypt the string "The Quick Brown Fox Jumps Over The Lazy Dog" in ROT13: | |||
<source lang="bash"> | |||
$ # Map upper case A-Z to N-ZA-M and lower case a-z to n-za-m | |||
$ echo "The Quick Brown Fox Jumps Over The Lazy Dog" | tr 'A-Za-z' 'N-ZA-Mn-za-m' | |||
Gur Dhvpx Oebja Sbk Whzcf Bire Gur Ynml Qbt | |||
$ tr 'A-Za-z' 'N-ZA-Mn-za-m' <<<"The Quick Brown Fox Jumps Over The Lazy Dog" | |||
Gur Dhvpx Oebja Sbk Whzcf Bire Gur Ynml Qbt | |||
</source> | |||
and the same string for ROT47: | |||
<source lang="bash"> | |||
$ echo "The Quick Brown Fox Jumps Over The Lazy Dog" | tr '\!-~' 'P-~\!-O' | |||
%96 "F:4< qC@H? u@I yF>AD ~G6C %96 {2KJ s@8 | |||
</source> | |||
and | |||
<source lang="bash"> | |||
$ tr '\!-~' 'P-~\!-O' <<<"The Quick Brown Fox Jumps Over The Lazy Dog" | |||
%96 "F:4< qC@H? u@I yF>AD ~G6C %96 {2KJ s@8 | |||
</source> | |||
In the [[Vim (text editor)|Vim text editor]], one can ROT13 a selection with the command:<ref>[http://www.rayninfo.co.uk/vimtips.html Best of VIM Tips, gVIM's Key Features zzapper]</ref> | |||
<source lang="vim"> | |||
g? | |||
</source> | |||
==See also== | |||
* [[Cryptanalysis]] | |||
==References== | |||
{{Reflist|50em}} | |||
==External links== | |||
<!-- DO NOT ADD ANY MORE IMPLEMENTATIONS --> | |||
* [http://rot13.de/ Online Converter] for ROT5 and ROT13 (no [[JavaScript]]) | |||
* [http://cryptii.com/text/rot13 Convert to or from ROT5, ROT13, ROT18, ROT47] (using [[JavaScript]]) | |||
<!-- DO NOT ADD ANY MORE IMPLEMENTATIONS --> | |||
{{Cryptography navbox | classical}} | |||
{{Use dmy dates|date=September 2010}} | |||
{{DEFAULTSORT:Rot13}} | |||
[[Category:Classical ciphers]] | |||
{{Link GA|de}} | |||
{{Link GA|es}} | |||
{{Link GA|zh}} | |||
Revision as of 10:42, 16 January 2014
ROT13 ("rotate by 13 places", sometimes hyphenated ROT-13) is a simple letter substitution cipher that replaces a letter with the letter 13 letters after it in the alphabet. ROT13 is an example of the Caesar cipher, developed in ancient Rome.
In the basic Latin alphabet, ROT13 is its own inverse; that is, to undo ROT13, the same algorithm is applied, so the same action can be used for encoding and decoding. The algorithm provides virtually no cryptographic security, and is often cited as a canonical example of weak encryption.
ROT13 is used in online forums as a means of hiding spoilers, punchlines, puzzle solutions, and offensive materials from the casual glance. ROT13 has been described as the "Usenet equivalent of a magazine printing the answer to a quiz upside down".[1] ROT13 has inspired a variety of letter and word games on-line, and is frequently mentioned in newsgroup conversations.
Description
Applying ROT13 to a piece of text merely requires examining its alphabetic characters and replacing each one by the letter 13 places further along in the alphabet, wrapping back to the beginning if necessary.[2] A becomes N, B becomes O, and so on up to M, which becomes Z, then the sequence continues at the beginning of the alphabet: N becomes A, O becomes B, and so on to Z, which becomes M. Only those letters which occur in the English alphabet are affected; numbers, symbols, whitespace, and all other characters are left unchanged. Because there are 26 letters in the English alphabet and 26 = 2 × 13, the ROT13 function is its own inverse:[2]
In other words, two successive applications of ROT13 restore the original text (in mathematics, this is sometimes called an involution; in cryptography, a reciprocal cipher).
The transformation can be done using a lookup table, such as the following:
| ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz |
| NOPQRSTUVWXYZABCDEFGHIJKLMnopqrstuvwxyzabcdefghijklm |
For example, in the following joke, the punchline has been obscured by ROT13:
How can you tell an extrovert from an introvert at NSA? Va gur ryringbef, gur rkgebireg ybbxf ng gur BGURE thl'f fubrf.
Transforming the entire text via ROT13 form, the answer to the joke is revealed:
Ubj pna lbh gryy na rkgebireg sebz na vagebireg ng AFN? In the elevators, the extrovert looks at the OTHER guy's shoes.
A second application of ROT13 would restore the original.
Usage
ROT13 was in use in the net.jokes newsgroup by the early 1980s.[3] It is used to hide potentially offensive jokes, or to obscure an answer to a puzzle or other spoiler.[2][4] A shift of thirteen was chosen over other values, such as three as in the original Caesar cipher, because thirteen is the value for which encoding and decoding are equivalent, thereby allowing the convenience of a single command for both.[4] ROT13 is typically supported as a built-in feature to newsreading software.[4] Email addresses are also sometimes encoded with ROT13 to hide them from less sophisticated spam bots.
ROT13 is an example of the encryption algorithm known as a Caesar cipher, attributed to Julius Caesar in the 1st century BC.[5]
ROT13 is not intended to be used where secrecy is of any concern—the use of a constant shift means that the encryption effectively has no key, and decryption requires no more knowledge than the fact that ROT13 is in use. Even without this knowledge, the algorithm is easily broken through frequency analysis.[2] Because of its utter unsuitability for real secrecy, ROT13 has become a catchphrase to refer to any conspicuously weak encryption scheme; a critic might claim that "56-bit DES is little better than ROT13 these days". Also, in a play on real terms like "double DES", the terms "double ROT13", "ROT26", or "2ROT13" crop up with humorous intent, including a spoof academic paper "On the 2ROT13 Encryption Algorithm".[6] As applying ROT13 to an already ROT13-encrypted text restores the original plaintext, ROT26 is equivalent to no encryption at all. By extension, triple-ROT13 (used in joking analogy with 3DES) is equivalent to regular ROT13.
In December 1999, it was found that Netscape Communicator used ROT-13 as part of an insecure scheme to store email passwords.[7] In 2001, Russian programmer Dimitry Sklyarov demonstrated that an eBook vendor, New Paradigm Research Group (NPRG), used ROT13 to encrypt their documents; it has been speculated that NPRG may have mistaken the ROT13 toy example—provided with the Adobe eBook software development kit—for a serious encryption scheme.[8] Windows XP uses ROT13 on some of its registry keys.[9]
The ROT13 encryption is used to cipher cache hints on Geocaching.com.
Letter games and net culture
| abcdefghijklmnopqrstuvwxyz NOPQRSTUVWXYZABCDEFGHIJKLM | |
| aha ↔ nun | ant ↔ nag |
| balk ↔ onyx | bar ↔ one |
| barf ↔ ones | be ↔ or |
| bin ↔ ova | ebbs ↔ roof |
| envy ↔ rail | er ↔ re |
| errs ↔ reef | flap ↔ sync |
| fur ↔ she | gel ↔ try |
| gnat ↔ tang | irk ↔ vex |
| clerk ↔ pyrex | purely ↔ cheryl |
| PNG ↔ cat | SHA ↔ fun |
| furby ↔ sheol | terra ↔ green |
| what ↔ Jung | URL ↔ hey |
| purpura ↔ Chechen | shone ↔ FUBAR |
| Ares ↔ Nerf | abjurer ↔ nowhere |
ROT13 provides an opportunity for letter games. Some words will, when transformed with ROT13, produce another word. The longestTemplate:Fact example in the English language is the pair of 7-letter words abjurer and nowhere; there is also the 7-letter pair Chechen and purpura. Other examples of words like these are shown in the table.[10] The pair gnat and tang are an interesting example which are both ROT13 reciprocals and (taken together) a palindrome.
The 1989 International Obfuscated C Code Contest (IOCCC) included an entry by Brian Westley. Westley's computer program can be encoded in ROT13 or reversed and still compiles correctly. Its operation, when executed, is either to perform ROT13 encoding on, or to reverse its input.[11]
The newsgroup alt.folklore.urban coined a word—furrfu—that was the ROT13 encoding of the frequently encoded utterance "sheesh". "Furrfu" evolved in mid-1992 as a response to postings repeating urban myths on alt.folklore.urban, after some posters complained that "Sheesh!" as a response to newcomers was being overused.[12]
Variants
ROT5 is a practice similar to ROT13 that applies to numeric digits (0 to 9). ROT13 and ROT5 can be used together in the same message.
ROT47 is a derivative of ROT13 which, in addition to scrambling the basic letters, also treats numbers and common symbols. Instead of using the sequence A–Z as the alphabet, ROT47 uses a larger set of characters from the common character encoding known as ASCII. Specifically, the 7-bit printable characters, excluding space, from decimal 33 '!' through 126 '~', 94 in total, taken in the order of the numerical values of their ASCII codes, are rotated by 47 positions, without special consideration of case. For example, the character A is mapped to p, while a is mapped to 2. The use of a larger alphabet produces a more thorough obfuscation than that of ROT13; for example, a telephone number such as +1-415-839-6885 is not obvious at first sight from the scrambled result Z`\c`d\gbh\eggd. On the other hand, because ROT47 introduces numbers and symbols into the mix without discrimination, it is more immediately obvious that the text has been enciphered.
Example:
- The Quick Brown Fox Jumps Over The Lazy Dog.
enciphers to
- %96 "F:4< qC@H? u@I yF>AD ~G6C %96 {2KJ s@8]
The GNU C library, a set of standard routines available for use in computer programming, contains a function—memfrob()[13]—which has a similar purpose to ROT13, although it is intended for use with arbitrary binary data. The function operates by combining each byte with the binary pattern 00101010 (42) using the exclusive or (XOR) operation. This effects a simple XOR cipher. Like ROT13, memfrob() is self-reciprocal, and provides a similar, virtually absent, level of security.
Implementation
The ROT13 and ROT47 are fairly easy to implement using the Unix terminal application tr; to encrypt the string "The Quick Brown Fox Jumps Over The Lazy Dog" in ROT13:
$ # Map upper case A-Z to N-ZA-M and lower case a-z to n-za-m
$ echo "The Quick Brown Fox Jumps Over The Lazy Dog" | tr 'A-Za-z' 'N-ZA-Mn-za-m'
Gur Dhvpx Oebja Sbk Whzcf Bire Gur Ynml Qbt
$ tr 'A-Za-z' 'N-ZA-Mn-za-m' <<<"The Quick Brown Fox Jumps Over The Lazy Dog"
Gur Dhvpx Oebja Sbk Whzcf Bire Gur Ynml Qbt
and the same string for ROT47:
$ echo "The Quick Brown Fox Jumps Over The Lazy Dog" | tr '\!-~' 'P-~\!-O'
%96 "F:4< qC@H? u@I yF>AD ~G6C %96 {2KJ s@8
and
$ tr '\!-~' 'P-~\!-O' <<<"The Quick Brown Fox Jumps Over The Lazy Dog"
%96 "F:4< qC@H? u@I yF>AD ~G6C %96 {2KJ s@8
In the Vim text editor, one can ROT13 a selection with the command:[14]
g?
See also
References
43 year old Petroleum Engineer Harry from Deep River, usually spends time with hobbies and interests like renting movies, property developers in singapore new condominium and vehicle racing. Constantly enjoys going to destinations like Camino Real de Tierra Adentro.
External links
- Online Converter for ROT5 and ROT13 (no JavaScript)
- Convert to or from ROT5, ROT13, ROT18, ROT47 (using JavaScript)
30 year-old Entertainer or Range Artist Wesley from Drumheller, really loves vehicle, property developers properties for sale in singapore singapore and horse racing. Finds inspiration by traveling to Works of Antoni Gaudí.
Template:Link GA Template:Link GA Template:Link GA
- ↑ Template:Cite web
- ↑ 2.0 2.1 2.2 2.3 20 year-old Real Estate Agent Rusty from Saint-Paul, has hobbies and interests which includes monopoly, property developers in singapore and poker. Will soon undertake a contiki trip that may include going to the Lower Valley of the Omo.
My blog: http://www.primaboinca.com/view_profile.php?userid=5889534 - ↑ Early uses of ROT13 found in the Google USENET archive date back to 8 October 1982, posted to the net.jokes newsgroup [1][2].
- ↑ 4.0 4.1 4.2 Template:Cite web
- ↑ 20 year-old Real Estate Agent Rusty from Saint-Paul, has hobbies and interests which includes monopoly, property developers in singapore and poker. Will soon undertake a contiki trip that may include going to the Lower Valley of the Omo.
My blog: http://www.primaboinca.com/view_profile.php?userid=5889534 - ↑ Template:Cite web
- ↑ Template:Cite web
- ↑ Template:Cite web
- ↑ Template:Cite web
- ↑ Template:Cite web
- ↑ Template:Cite web
- ↑ Template:Cite web
- ↑ Template:Cite web
- ↑ Best of VIM Tips, gVIM's Key Features zzapper
